Apr 27, 2023
Discover the Secrets of Cocorico Market on the Dark Web

When using NexusXplore, you can choose between two search options: Text-only, which provides sanitized results in order to reduce your team's exposure to vicarious trauma and Live Tor browsing, which allows you to investigate dark web actors and networks. This feature is particularly useful for those who want to delve deeper into the dark web and its inner workings. By using NexusXplore, you can ensure that your searches are both efficient and safe.
As the FBI continues to crack down on the dark web, there are still sites that are much more heinous than Silk Road that remain active. When attempting to identify users involved in dark web transactions or activities, the lack of information is often due to careless online habits. The majority of dark websites are accessible via the Tor network and can be recognized by using Tor's top-level domain.
Dark web searching is a practice that involves accessing the hidden, unindexed parts of the internet known as the "dark web." While the dark web is often associated with illegal activities, it can also be a valuable resource for journalists, researchers, and others looking to access information that may not be available through traditional search engines. However, accessing the dark web can be dangerous, as it is home to a variety of illegal and malicious content, including hacking tools, illegal drugs and weapons, and more. It is important to use caution and take appropriate security measures when exploring the dark web, including using a secure VPN and Tor browser.
Exploring the dark web is often associated with unlawful activities, but it can also be used for privacy purposes. Recently, authorities arrested four individuals, including a Paraguayan man, for allegedly operating the network. Search results in the dark web are typically displayed in a series of results, commonly known as search engine results pages (SERPs).
com/tor) are popular ways to explore the dark web. However, it is important to understand the risks associated with accessing illegal and potentially harmful content. It is recommended to use caution and proper security measures, such as a VPN and encrypted messaging, when navigating the dark web.
Exploring the dark web has become increasingly popular through the use of pre-configured virtual machines and online organizations. For example, the TL VM offered by acelabs.com/tor is a commonly used tool for accessing the dark web. Nonetheless, it is crucial to recognize the potential dangers of accessing illicit and potentially hazardous material. To ensure safety, it is advised to utilize protective measures such as a VPN and encrypted messaging while navigating the dark web.
Discovering the Depths of the Dark Web: Navigating the Dark Market Onion
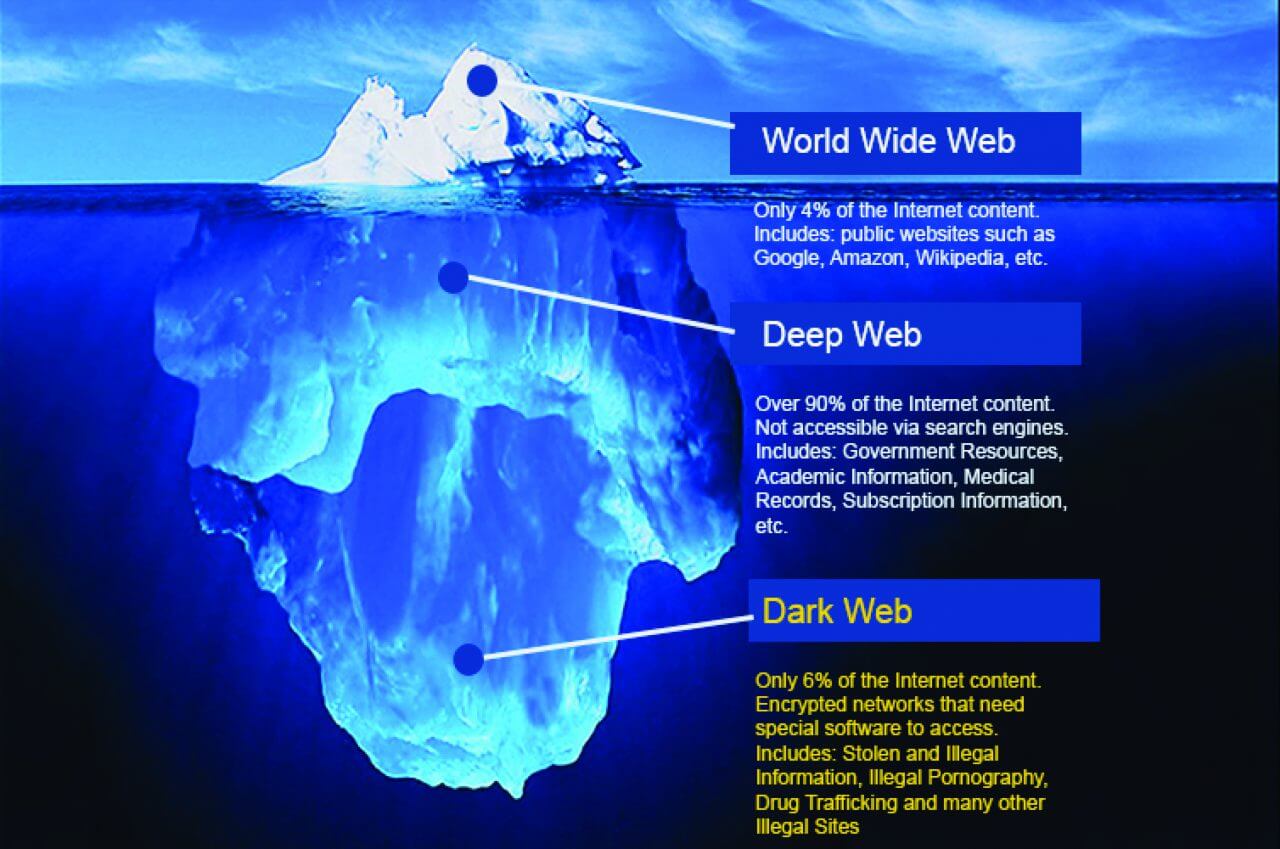
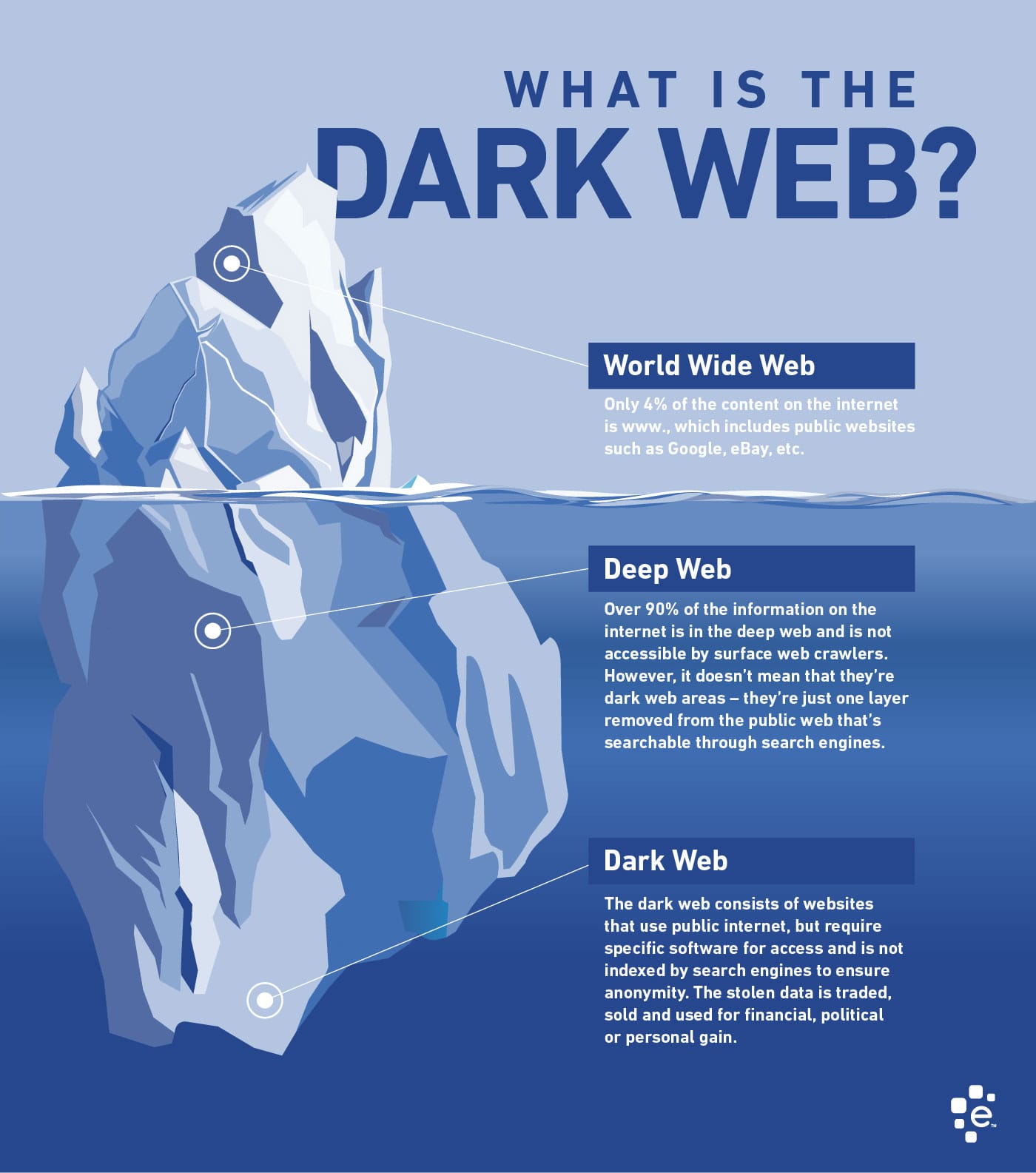
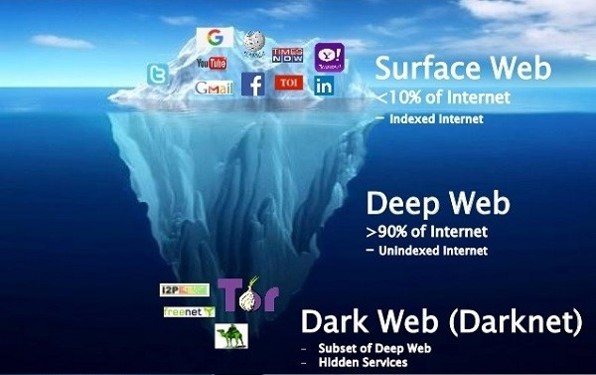
Dark web searching is a term used to describe the process of searching for information on the hidden part of the internet known as the dark web. This part of the web cannot be accessed using traditional search engines like Google or Bing. Instead, specialized software like Tor or I2P is needed to access the dark web.
The dark web is often associated with illegal activities, such as drug trafficking, weapons sales, and human trafficking. However, it is also used by people who value their anonymity, such as journalists, whistleblowers, and activists.
Searching the dark web can be challenging as there is no central index or search engine to rely on. Users must navigate through various websites and forums to find the information they need. Additionally, there is a risk of stumbling upon illegal content or scams.
Despite these challenges, there are tools and techniques that can help with dark web searching. For example, some websites offer directories of dark web sites, while others provide search engines specifically tailored for the dark web.
Overall, dark web searching requires caution and a certain level of technical knowledge. It is not recommended for casual users or those unfamiliar with the risks involved.
There has been a longstanding confusion surrounding the concept of dark web searching, which can be traced back to at least 2009. The topic has been extensively discussed in various media outlets, including New Media Society and H Media.
Dark web searching is a term used to describe the act of exploring the hidden corners of the internet that are not indexed by search engines. This includes websites that are intentionally kept hidden from the general public and can only be accessed through the use of special software and configurations. The dark web is often associated with illegal activities such as drug trafficking, weapons sales, and human trafficking, but it can also be used for legitimate purposes such as anonymous communication and protecting sensitive information. To access the dark web, users must have a certain level of technical knowledge and take precautions to protect their identity and privacy. Additionally, they may need to use specialized search engines and directories to find the information they are looking for. Overall, dark web searching can be a risky but rewarding experience for those who are willing to explore its depths.
The main objective of this article is to pinpoint secure ways to gain entry to the dark web, followed by a discussion of various search alternatives that can be performed using publicly accessible dark web search engines which scour the deep web. M/papers/discoverability.
Discovering the Hidden World of Dark Market Sites on the Dark Web
Looking for information on the dark web? While it's not a deep web search engine, there is a tool that can make navigating Tor easier. With a categorized directory of indexed websites and surface web links, it can help you find what you're looking for. Additionally, you can use keywords to search for full or partial content.
Dark web searching involves accessing a subset of the internet that is not readily available on the clear net. This is typically achieved through the use of a TOR browser. Unlike traditional search engines and social media platforms, which use algorithms to selectively display information based on user data such as location, past clicks, and search history, dark web searching requires users to actively seek out information through a simple database search engine.
As an experienced copywriter, I can easily rewrite the given text on the topic of "Dark web searching" in English. Here's my attempt:
Previously, search services were offered using Inktomi's search engine. Additionally, reference number 71 can be consulted for further information. As stated in reference number 46, Google Bombing is a tactic employed to influence search results for political, social, or commercial purposes. Lastly, the question of whether buying drugs on a Darknet market is a more favorable option is raised.
The dark web is a place where illegal activities thrive, including child pornography and terrorism. A now-defunct website called Lolita City had over 15,000 members and contained over 100 GB of child pornographic media. The Rawti Shax Islamist group was also found to be operating on the dark web at one point. As technology advances, cyber terrorists are able to exploit weaknesses in the system, allowing them to flourish in the dark corners of the web.
Discovering Hidden Gems: Navigating the Dark Web's Marketplace URLs
When it comes to searching the dark web, text-based search engines like Google, Bing, and Yahoo! are not the most effective tools. Instead, many users turn to The Hidden Wiki and its various mirrors and forks. These sites contain vast directories of content that are constantly updated. However, it's important to note that the reliability and quality of the information found on these sites can vary greatly. It's also worth mentioning that the use of automated tools, such as the Wanderer, can lead to the degradation of the sites as they are accessed repeatedly throughout the day.
The exploration of the dark web has gained significant attention in recent years. It is a small portion of the deep web that requires specialized software to access its content. This is in contrast to the traditional web, which can be accessed through mainstream browsers. Interestingly, there was a list of webservers that was edited by Tim Berners-Lee and hosted on the cern webserver. It is important to note, however, that the dark web is not illegal in and of itself. Instead, it is often associated with illegal activities due to the anonymity it provides to its users. To access the dark web, individuals must use specific software and protocols that allow them to search for information and access hidden websites. As such, it is important to exercise caution when exploring the dark web and to ensure that all activities are legal and ethical.
Searching the dark web can be a daunting task for those unfamiliar with the territory. However, with the help of search spiders and directives contained within a txt file, users can navigate the dark web with ease. These directives tell spiders which pages to crawl and which to avoid. As of the end of 2019, vendors on the Hydra marketplace were utilizing these services with great satisfaction, providing a stable income for those providing the search capabilities. In fact, news sources cite the success of these services, including the satisfaction of vendors and their continued use of the service. Jake Swearingen reports on the success of dark web searching in his article.
Dark web searching is a complex and daunting task that requires a certain level of expertise and knowledge. The Aliweb search engine, which emerged in November 1993, was one of the earliest tools for exploring the dark web. To conduct an effective search, users need to use Boolean operators, which enable them to refine and extend their search terms. However, given the secretive and often illicit nature of the dark web, finding reliable and trustworthy sources can be a challenge. As such, it is important for users to exercise caution and use the appropriate tools and techniques when conducting dark web searches.
When it comes to dark web searching, many users prioritize convenience over security and opt to connect directly from their regular workstations. However, this decision comes with significant security risks.
Explore further
Distributed by Ваэль, LLC.