Apr 22, 2023
The Future of Dark Web Drug Markets: Accessing the Underbelly of the Internet in 2023
Accessing the dark web can be achieved by utilizing open-source encryption software like Veracrypt. It is possible to purchase legitimate products and services on the dark web, but it's important to keep in mind that anonymity is reciprocal. To ensure your safety, exercise caution and use a combination of the Tor browser and common sense when accessing dark web sites. With these measures in place, the dark web can be safely navigated.
The primary objective was to provide ships with the ability to communicate with one another and their headquarters without disclosing their whereabouts. Accessing the dark web may prove hazardous, and it might not be suitable for everyone.
Discover the Secrets of the Dark Web Gun Marketplace
Accessing the dark web can be a risky venture as your personal data is being stored and you can only hope that companies are adhering to GDPR standards and keeping it safe through encryption and other methods. With billions of sites and addresses, it's incredible that we can seek out and discover virtually anything. Fortunately, we will soon be broadening access to our dark web report to select international markets.
When you are not connected to any networks, your data cannot be intercepted remotely.
The Tor browser has the ability to keep your true location hidden by directing your traffic through multiple relays. Data brokers, like LocalBlox, scour the internet to gather information about businesses and consumers to sell for marketing purposes. To accomplish this, they route users' and websites' traffic through a series of relays to obscure their location.
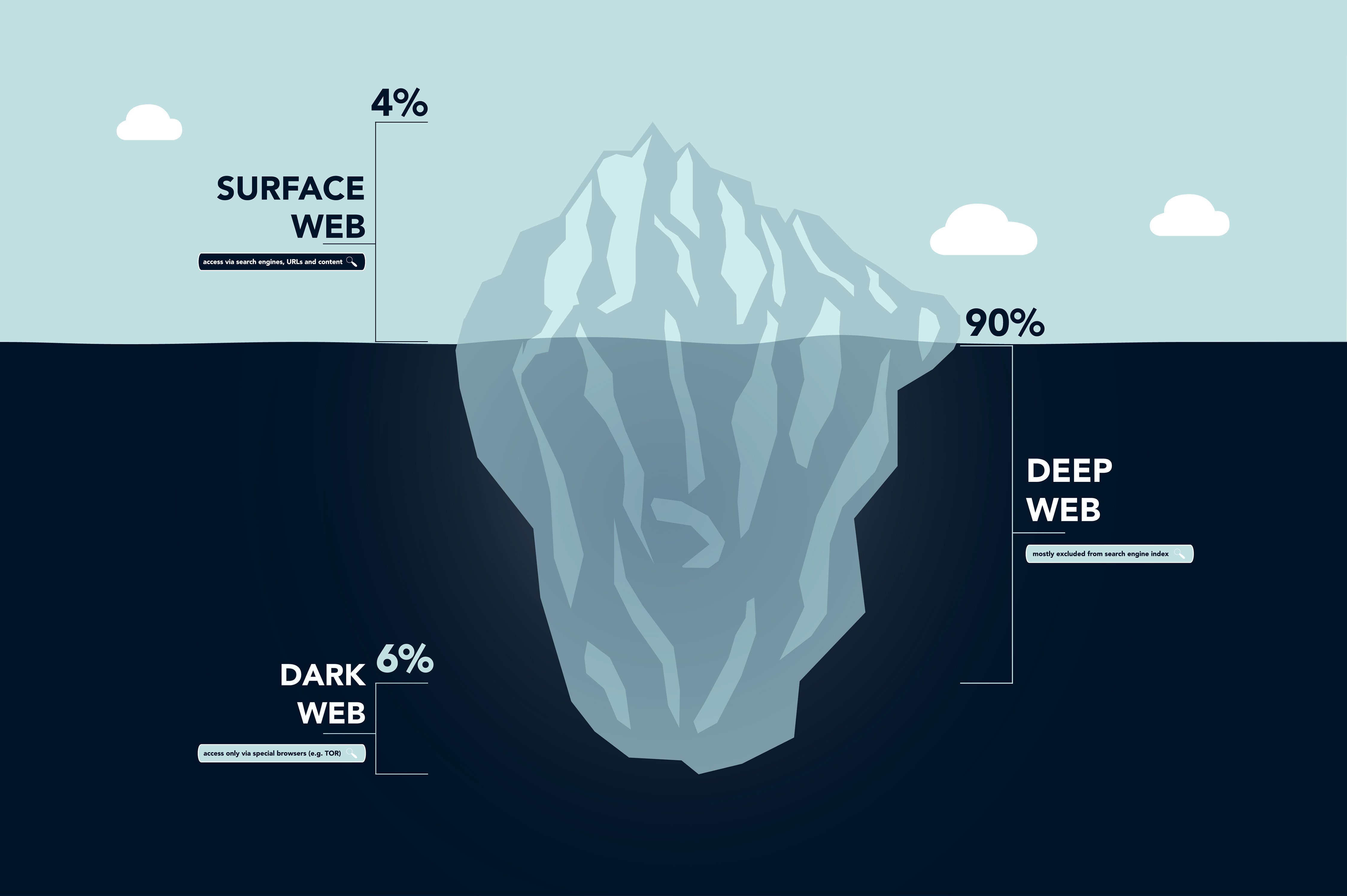
Accessing the dark web provides a gateway to a world of hidden information and activities that are not easily accessible through traditional search engines. This includes a variety of illegal goods and services, as well as a network of anonymous communication channels that allow users to remain anonymous. However, it's important to note that not all content on the dark web is illegal or harmful. In fact, the deep web also encompasses academic content that is handled directly by universities, providing a wealth of knowledge and research that may not be readily available through other channels.
"Inside the Shadowy World of the Dark Web Hitmen"
The level of safety you require determines your access to the dark web. Although incidents do occur on this hidden part of the internet, they are merely a small part of the overall picture.
Undoubtedly, there exist numerous Tor-exclusive websites that provide access to illegal drugs or materials. Web crawlers can effortlessly scan through these sites and their associated links, capturing them in the process. Is it advisable to use both a VPN and Tor for accessing these sites?
By having access to the dark web, we can enhance our capability to detect and distinguish websites that have been compromised. This enables us to detect a greater number of attacks and prevent an extra 25 phishing attempts on Chrome and Android every month, significantly improving our security measures.
Unlock the Secrets of the Dark Web with Simple Login
If you have been searching for a surprise gift at a store recently, you can easily delete it from your browsing history. However, Google is taking things a step further by introducing new tools that offer you more control. This includes dark web scans for your Gmail address, which was only available to Google One subscribers in the United States. But now, Google is expanding access to the dark web report to more users access to dark web in the future.
The dark web is a favored destination for con artists due to its anonymity and lack of regulation. Additionally, a fresh Data deletion zone has been incorporated into the Google Play Data security section of certain applications, streamlining the process of requesting the deletion of personal account information or other data.
When a business decides to store their documents on an Amazon web server, they are essentially entering the deep web. However, for those who crave added protection, utilizing a VPN before accessing the dark web through the Tor browser offers an extra layer of security that cannot be achieved with Tor alone.
Facebook provides a way to access their services, but it can be challenging to log in due to the frequent appearance of a different location every time. However, utilizing the Tor browser appropriately allows users to remain anonymous and visit exclusive forums where they can make purchases using untraceable cryptocurrencies. The Tor browser employs a router to bounce your signal across other Tor users globally, effectively providing a pseudo-anonymity while accessing the dark web.
Access to the dark web is not only sought after by conspiracy theorists who believe the government is constantly monitoring them, but also by political activists, dissidents, journalists, and individuals who are wary of websites misusing their personal information.
Explore further
Distributed by subeaki, LLC.